Employee of the Month

Please select your nomination for employee of the month. An employee cannot nominate themselves. All Employees are eligible.
Employee Checklist
Follow this checklist to be entered in a drawing for a $25 gift card! For the month of May.
Newsletter Trivia

PS. Follow and like any of our social posts to boost that $25 up to $30!
Spotting the Fakes: Deep Dive into Deep Fakes and Their Role in Cybercrime

Phishing tactics have been a persistent threat for years, and with the ever-changing digital landscape, we can always count on cyber criminals to stay updated. We have talked about many phishing tactics in the past, however 2024 has brought a new tactic that feeds on the power of AI.
Shedding Light on the Dark: The Influence of the Dark Web on Cybersecurity
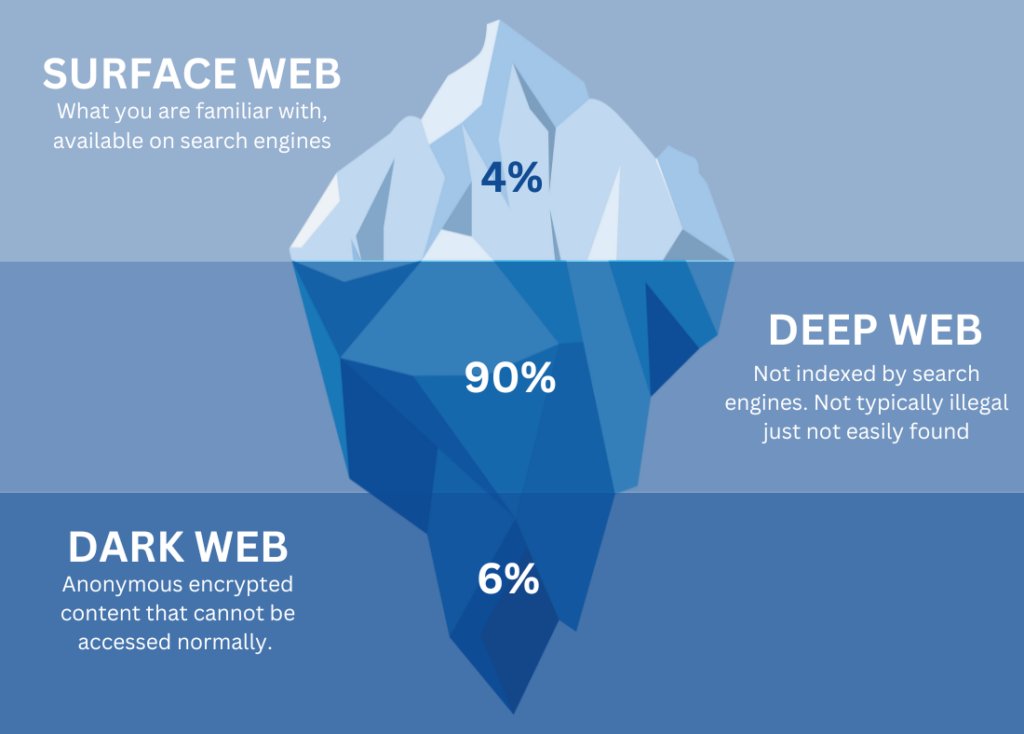
Chances are, you are familiar with the dark web. Whether it be from news stories or your favorite crime TV show. You may understand that it is used for more serious criminal activities, but beyond the headlines and portrayals there is a crime that is often overlooked.
Why IT Often Bears the Brunt of Cyber Security Breaches

After a Cyber Security breach, it’s common for the blame to automatically fall on IT. Of course, there are many steps that need to be taken to help prevent Cyber Attacks, but nothing is ever guaranteed. So why is everyone so quick to blame IT? Visible Role in Technology Infrastructure: IT is responsible for […]